Neustar Highlights Increase in Ransom-Relevant DDoS Attacks and Bigger Use of Present Attack Vectors
Neustar, Inc., a global data expert services and know-how business and chief in identity resolution, currently released its report entitled ‘Cyber Threats and Developments: Pandemic Style’, detailing the safety threats faced by firms as the COVID-19 pandemic accelerated the digital revolution.
This press release features multimedia. See the total release here: https://www.businesswire.com/information/home/20210128005282/en/
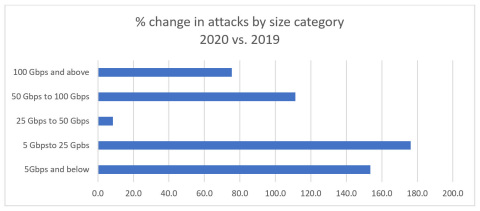
Figure 1: Share transform in variety of assaults by sizing class, 2020 vs. 2019 (Graphic: Business enterprise Wire)
Educated by knowledge from Neustar’s Security Functions Centre (SOC), the report reveals a 154 per cent maximize in the quantity of attacks between 2019 and 2020, with expansion in ransom-similar DDoS (RDDoS) attacks and a increase in use of present assault vectors, such as website programs. The report also supplies critical details all around the quantity, dimension, length, and intensity of DDoS assaults during 2020 to maintain cyber security specialists informed.
DDoS Ransom Attacks on the Increase
Primarily, the report highlights a rise in ransom-linked DDoS attacks, by which extortion demands are issued from companies. These assaults grew in persistence and sophistication, as properly as by goal, compared to past many years.
While RDDoS is not a new phenomenon for numerous on the web industries, attackers have recently established their sights on businesses across a broader assortment of sectors including monetary solutions, federal government, and telecommunications.
A person cause for the adoption of DDoS as a ransom vector, as opposed to employing malware, is the simplicity with which this kind of assaults can be carried out. Infecting an organization’s networks with malware or ransomware can take time and very careful organizing. Launching a DDoS attack, in comparison, has grow to be relatively simple and has the included advantage of getting more difficult to trace again to its origin.
2020 observed bad actors posing as prolific risk teams these as Fancy Bear in ransom notes – capitalizing on dread of higher-profile nation-state attacks – and threatening DDoS attacks unless the ransom was paid out in just a certain time body.
“Organizations ought to keep away from having to pay these ransoms,” mentioned Michael Kaczmarek, Vice President of Stability Merchandise Administration at Neustar. “Instead, any attack must be noted to the closest regulation enforcement area workplace, as the information and facts may well support establish the attackers and ultimately keep them accountable. Over and above this, businesses can put together by location up a strong DDoS mitigation tactic, which includes examining the risks, evaluating offered remedies, taking into consideration mitigation approaches and retaining their program and provider up to day.”
Current assault vectors
Although 2020 did not see any significantly new assault vectors arise, there was unquestionably a bigger use of current kinds like net programs, which ended up the prime specific hacking vector in 2020.
Numerous crafted-in accessibility protocols, which have been progressively exploited as attack vectors, arrived up yet again in 2020. In reality, the FBI issued an alert in July warning that typical network protocols like ARMS (Apple Remote Administration Expert services), WS-DD (Web Expert services Dynamic Discovery) and CoAP (Constrained Software Protocol) were becoming abused by hackers to conduct DDoS reflection and amplification assaults – when cautioning that disabling them could trigger a decline in business enterprise productiveness and connectivity.
In response to this heightened threat level, the outcomes of the hottest Neustar International Protection Council (NISC) survey indicated that additional cyber security professionals are outsourcing DDoS mitigation, getting greater by a comprehensive percentage place in the very last quarter by yourself.
DNS assaults
In 2020, Neustar also observed an increase in assaults on the Domain Name Procedure itself — or what glance like assaults, as terrible actors abuse the method.
“Acting as the Internet’s tackle ebook and spine of today’s digital products and services, it’s unsurprising that DNS is an progressively interesting goal for malicious actors, particularly as additional consumers transform to web-sites in the course of peak on the net searching periods,” stated Rodney Joffe, Senior Vice President and Fellow, Neustar.
Latest NISC study information supports this craze, with a few in 5 respondents in a December 2020 examine reporting they experienced fallen target to a DNS attack in the final 12 months. Even a lot more concerning, above 70 p.c of businesses admitted to acquiring reservations about their consciousness of, and capacity to respond to, DNS attacks.
The total variety of DDoS attacks Neustar mitigated on behalf of its customers in 2020 increased by extra than two and a 50 percent moments more than 2019. The largest assault sizing noticed for the duration of this time was also the largest that Neustar has at any time mitigated and, at 1.17 Terabits for every next (Tbps), among the largest ever seen on the Internet. The longest period for a one attack was also the longest Neustar has mitigated, at 5 times and 18 several hours.
A duplicate of the Neustar report is offered listed here.
About Neustar
Neustar is an info solutions and engineering enterprise and a chief in identity resolution offering the information and technological innovation that empower dependable connections concerning businesses and persons at the times that make any difference most. Neustar offers sector-major alternatives in promoting, danger, communications, and protection that responsibly link information on individuals, products and areas, continually corroborated through billions of transactions. Neustar serves much more than 8,000 clients around the globe, which include 60 of the Fortune 100. Learn how your firm can gain from the electrical power of dependable connections here: dwelling.neustar.
View supply model on businesswire.com: https://www.businesswire.com/information/property/20210128005282/en/
Contacts
Pete Johnson
Finn Partners for Neustar, Inc.
T. 503-546-7880





